
Naval intelligence along with Andhra Pradesh Police and Central intelligence agencies busted a spy network operating from Mumbai and Vishakhapatnam on December 20, last year. The case was handed over to NIA by home ministry after 7 people which included 6 Indian Naval personnel and a Hawala operator were arrested. Presently the number of people arrested in the case have surged to 13. This joint operation carried out by the intel agencies is called operation Dolphin’s nose.

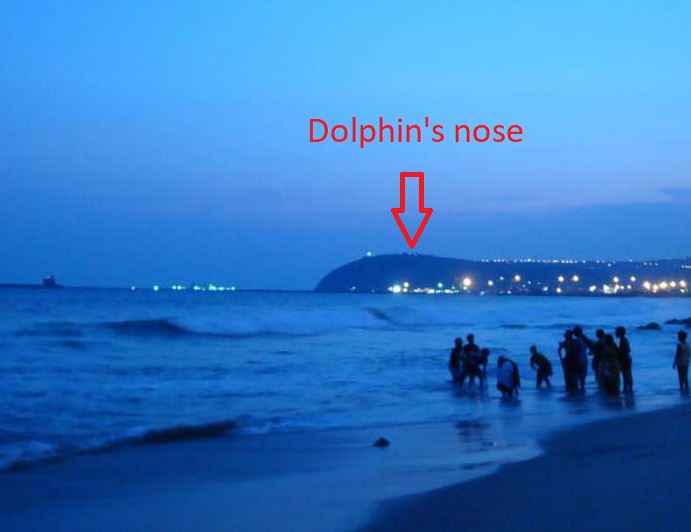
The operation Dolphin’s nose has been named after a hill by the same name located very close to Vizag port, where in early 19th century British and French Naval forces had fought the battle of Vizagapatam. Indian Naval personnel fell for one of the oldest tricks in the sleuth book—honey trap. The non-commissioned officers from the batch of 2017 were, ostensibly, befriended by different women on Facebook and lured into sharing explicit personal videos. This culminated with the naval personnel located in the western Naval command and Eastern Naval command, being blackmailed by the ISI agent, who was running different social media accounts masquerading as a female. Once trapped, the men were contacted by a Hawala operator, who collected information from the men, and deposited cash into their accounts for providing information. The naval headquarters located at Vishakhapatnam is strategically important dockyard for the 2 nuclear-powered submarines of India, ergo this case alarmed Indian Navy. Albeit, sources have confirmed that no substantial information was leaked to the enemy spy agency and the Indian Naval assets are safe.
It is not uncommon in espionages conducted by the enemy agents to use a honeypot or a honeytrap to entice a target into a false relationship. This helps the enemy in gleaning information through the target or it facilitates the enemy in gaining influence over the target, at times to an extent that the individual can be subverted to carry out an operation for the enemy agency, called sabotage in sleuth lexicon.
Indian Navy has been rocked by atleast 2 such espionage cases since early 2000’s. In 2001, five Naval officers including a chief security officer of Naval Armament Depot, Vishakhapatnam, were arrested for leaking information to ISI agents located in Nepal. Back then, police had revealed that the chief security officer Lieutenant commander Raj Kumar had received huge amount of sum in his bank accounts for the information he passed on to ISI. The officer had later committed suicide in the jail.
Another case of espionage that had come to light was Naval war room leak case in 2005, which involved many high profile naval officers and veterans. Apparently 7000 pages of sensitive information was from Naval war room and Air headquarters which had direct impact on nation’s security. The Rs 18,000 crore Scorpene submarine scam is also linked to Naval war room leak.
Indian Navy has now strictly instructed it’s men to use 2G phones at work and banned the use of smart phones in the Naval premises.
This article is written by Levina
Read similar espionage cases
Mole from Indian Border Force nabbed by Military Intel unit and ATS
Indian Tri services snap backbone of ISI network in India, unearths havala transaction worth crores


Leave a Reply